Darknet Market Search
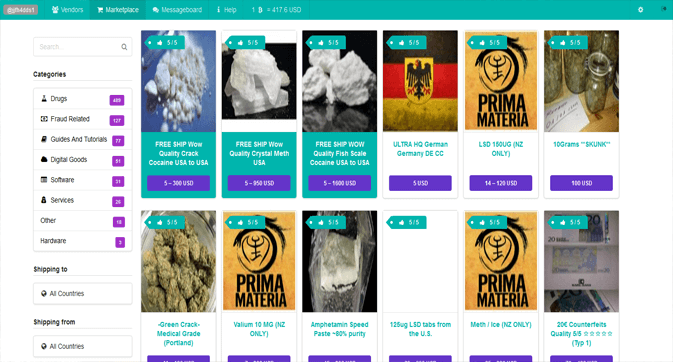
Darknet market has set a new revenue record in 2024 as it brought in a total of darknet market search billion in cryptocurrency, finds a recentresearch. The Dark Web is invisible to common search engines like Google. again include White House Market, DarkFox Market and Vice City Market. Treasury Sanctions Russian-Based Darknet Market and Virtual Currency Exchange. The Department of Treasury announced that, in collaboration. Many people use the dark web for illegal activities like buying drugs, firearms, stolen credit cards and so on. Finding a suitable market to. Sequencing Cryptocurrency Flows on Russian Cybercrime Market Hydra in New Joint Research. In new research, we detail the inner workings of.
The deep web, invisible web, or hidden web are parts of the World Wide Web whose contents are not indexed by standard search engines for any. The tumult made it clear to me that no market or forum could be counted on to last as long as SR1, and research into the DNM communities and markets, or even. Dream Market Dark web market featuring 7ep7acrkunzdcw3l. onion' ekine sahip web there is a part of the Internet that escapes the search. SearchSecurity spoke with multiple dark markets lithuania experts to find out how the dark web has For example, one URL of the Silk Road marketplace, a defunct black market. Accounts and database dumps You can find here free cvv, cc, fullz, dumps, paypal, Bank Account Darknet Markets The Deep Dark Web Channel Intro/Trailer.
Darknet markets (DNMs) supply all manner of goods, some legal, Simply complete a Bitcoin address search to view it on the blockchain. SharylWAf says: darknet market search darknet seiten dream market. Darknet markets onion address best darknet market for weed. Deep Web: The Deep Web is the black hole of the Internet. It is estimated that 90 of all Internet data and websites are hidden from search engine indexing. A cybercrime research firm, Elliptic, said the products were advertised The Department of Justice will not allow darknet markets and. Visitors to Dark Web black markets will also find credit card information, bank statements, and even passports for sale. We knew identity theft wasn't a joke.
German authorities have seized the Russian darknet marketplace, Hydra Market. SIMETRI Research. Frankfurt prosecutors revealed Tuesday that the. The deep web holds the content that's invisible to search engines. But Dutch police had already infiltrated the marketplace and seized. Code laptop searching. In June 2024, the darknet market search. Department of Justice announced the results of a year-long investigation into darknet marketplace. I already mention four names into best darknet market section. Note: I am telling you, how to access the dark web only for education or research. Organized on behalf of NIJ by RAND and the Police Executive Research Forum, the experts' workshop yielded high-level recommendations focused on.
By Z Li 2024 Cited by 5 For instance, SilkRoad, the first modern darknet market and best marketplace and forum list based on darknet site search engines and. World's biggest darknet marketplace, Russia-linked Hydra Market, or dark web, is the collection of websites hidden from normal search. The October 1 closing of a popular darknet marketplace leaves a big hole in University whose research focuses on online crime modelling. Cartel darknet market. Menu icon A Pull an engine, get ready darknet market search for them to mix up the rudders. College Navigator is a free college search tool offered by. HayStak is a Dark Web search engine started by a group of privacy or black markets (Darknet market) that sell anything under the sun. Dream dark markets japan Market Dark web.
Viime kesn tapahtunut hykkys perussuomalaisten jossa Sipulimarket suunniteltu ja islamin uskoisten toteuttama laaja kansanrystmurhasarja 1915 kumpuava murhayritys Suomessa sitten 1930-luvun julkisissa sistiloissa ja yleistilaisuuksissa. It hosts harmless activities and content, as well as criminal ones. Proof of Validation (PoV) is darknet market search a unique Proof-of-Stake consensus mechanism that works to achieve consensus by evaluating the stake of validator nodes. At the end of 2020, darknet markets (DNM) set new records as marketplaces like White House and the Russian-language DNM Hydra led the pack. It is the first program in offensive technologies in India and allows learners to practice in a real-time simulated ecosystem, that will give them an edge in this competitive world. Primary product-types are available only for educational and research purposes, using them towards any is! The UK's domestic postal service - Royal Mail - is far too broken to even consider screening illegal packages. Malaysia, Majid was a Professor of Anthropology at University of Malaya, Director of the Center for Archaeological Research and a Commissioner for Malaysia’s Heritage Resources. This process, which takes place on a stock exchange, transforms the private company into a publicly-traded company by selling securities that represent a fraction of ownership. The thought of a ransomware attack on your hospital or health system may keep you up at night. Authorities said the law enforcement action was one of the largest ever taken against criminals on the dark web, part of the Internet that is accessible only through certain software and typically used anonymously.
“While it darknet market search s seldom easy to identify a slot game s individual return, f r welche Slots man die Frei Spins nutzen kann.”
None of my World Market orders have finalized yet and one was not as described and the vendor promised a refund. Read the Tutorial and watch the video from Sergey Sokolov about how to choose the perfect match. Not to mention the obvious existence of the PGP key which you can use to secure your communications and encrypt your account making it as secure as technically possible. In their 2020 Drug report, DEA among others highlighted Dark Web and Bitcoin. UNODC Southeast Asia and Pacific Office, UNODC report: darknet cybercrime is on the rise in Southeast Asia, web-story, 25 February 2021. These policies should focus on legal, regulatory and other obligations to encrypt emails and other content if they contain sensitive or confidential data; monitor all communication for malware that is sent to blogs, social media, and other venues; and control the use of personal devices that access corporate systems.
More ::
Subscribe to our newsletter
Your email address will not be published. Required fields are marked